Services
Wireless Security Audit
Industry-leading Wireless Security Auditing
Find the gaps in your Wireless Cyber Security Posture
Identify security weaknesses and determine whether your wireless Cyber Security meets today’s standards

We get results
Our knowledge and deep expertise means we provide highly intelligent, tailored solutions that get results.

Experts that deliver
We have years of dedicated experience in installing WiFi solutions for organisations of all shapes and sizes.

Total peace of mind
If you have a problem with your WiFi, security or network, we’ll sort it. We guarantee we’ll find a solution.
Wireless Security Auditing
Wi-Fi
Security Audit
Wireless IoT
Security Audit
4G / 5G Mobile
Security Audit
LoRaWAN
Security Audit
Let’s get connected
We’ll find the solution, performance guaranteed. Get in touch to find out more.
Get startedWi-Fi and IoT Security Auditing
Wireless (in)Security
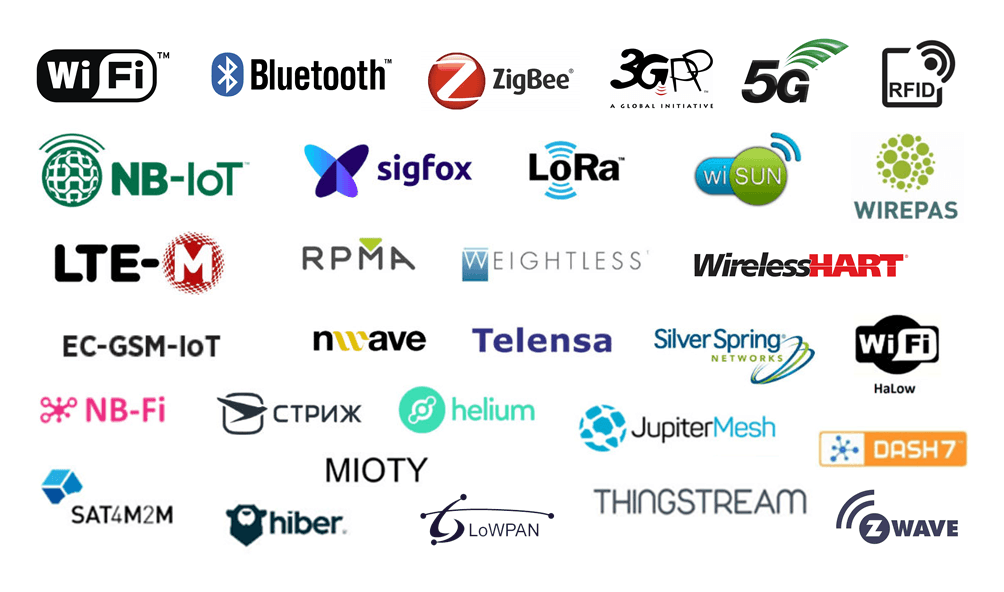
Here are just some of the wireless technologies that might be used in or around your organisation.
Does your organisation have devices that use or embed these wireless technologies? Are those devices secure, or are they offering direct or indirect access to your organisation’s systems and data?
How secure is your Wi-Fi network? Does it still use WPA2, WPA-PSK, MAC address filtering, SSID hiding or open / splash page access for guests?

Wireless Security Policy
A security policy is an organisation’s best weapon in defending against a possible breach or helping to restore a network and information if a breach has occurred.
We write detailed wireless security policy documents covering all manner of wireless systems, including 802.11 / Wi-Fi, Bluetooth, ZigBee, LoRaWAN, 4G, 5G and all wireless IoT protocols.
A robust Wireless Security Policy is a key part of your wireless Cyber Security.
Secure your organisation, and get peace of mind – speak with our Wireless Security team and see how we can help.
Testimonials
Don’t just take our word for it
Case Studies
See how Lever have helped business and organisations with their Wifi installation requirements.
Repair, Installation, Training & Support
Get Started
We’ll find the solution, performance guaranteed.
Get in touch to find out more.